The WordPress Welcart e-Commerce plugin (20,000+ active installations) fixed multiple information disclosure vulnerabilities affecting version 2.2.7 and below.
Unauthenticated Information Disclosure
CVSS v3.1: 7.5 (high)
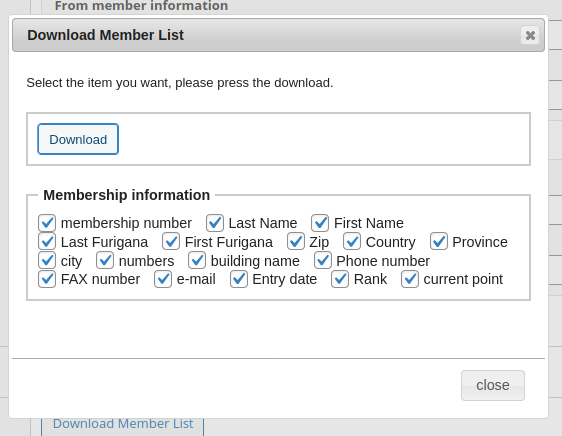
Welcart e-Commerce allows the administrator to download, in CSV format, three types of list: products, orders and members list.
Here’s an example of the data exported in the members list:
The related code can be found in the “usc-e-shop/extensions/DataListUpgrade/data_list_upgrade.php” script:
public function __construct() {
self::initialize_data();
if ( is_admin() ) {
add_action( 'usces_action_admin_system_extentions', array( $this, 'setting_form' ) );
add_action( 'init', array( $this, 'save_data' ) );
if ( self::$opts['orderlist_flag'] ) {
if ( isset( $_REQUEST['order_action'] ) && 'dlordernewlist' == $_REQUEST['order_action'] ) {
add_action( 'admin_init', array( $this, 'download_order_list' ) );
} elseif ( isset( $_REQUEST['order_action'] ) && 'dlproductnewlist' == $_REQUEST['order_action'] ) {
add_action( 'admin_init', array( $this, 'download_orderdetail_list' ) );
}
add_action( 'load-toplevel_page_usces_orderlist', 'usces_admin_order_list_hook' );
add_filter( 'screen_settings', 'usces_orderlist_screen_settings', 10, 2 );
add_filter( 'usces_admin_order_list', array( $this, 'change_orderlist' ) );
}
if ( self::$opts['memberlist_flag'] ) {
if ( isset( $_REQUEST['member_action'] ) && 'dlmembernewlist' == $_REQUEST['member_action'] ) {
add_action( 'admin_init', array( $this, 'download_member_list' ) );
}
add_action( 'load-welcart-management_page_usces_memberlist', 'usces_admin_member_list_hook' );
add_filter( 'screen_settings', 'usces_memberlist_screen_settings', 10, 2 );
add_filter( 'usces_admin_member_list', array( $this, 'change_memberlist' ) );
}
}
}
In the __construct method, the plugin registers the three actions (download_order_list, download_orderdetail_list and download_member_list) with the admin_init hook if the is_admin function returns true. As we’ve seen many times on this blog, neither admin_init nor is_admin can guarantee that the user is a logged-in administrator, they can be bypassed by an unauthenticated user accessing the “wp-admin/admin-ajax.php” or “wp-admin/admin-post.php” scripts for instance.
All three actions lack a capability check. An unauthenticated user can download the list of members, products and orders in CSV format.
Authenticated System Information Disclosure
CVSS v3.1: 4.3 (medium)
In “usc-e-shop/includes/default_filters.php” script, the plugin registers the usces_download_system_information AJAX action.
add_action( 'wp_ajax_usces_download_system_information', 'usces_download_system_information' );
The usces_download_system_information function is located in the “usc-e-shop/functions/function.php” script:
function usces_download_system_information(){
$filename = 'welcart_information_' . date_i18n('YmdHis') . '.txt';
$wp_environment = usces_get_wp_environment();
$environment = $wp_environment['environment'];
$theme = $wp_environment['theme'];
$active_plugins = $wp_environment['active_plugins'];
$inactive_plugins = $wp_environment['inactive_plugins'];
$welcart_information = get_welcart_system_information();
$loaded_extensions = get_loaded_extensions();
$ini_confs = ini_get_all();
$data = generate_system_information_text( $environment, $theme, $active_plugins, $inactive_plugins, $welcart_information, $loaded_extensions, $ini_confs);
$result = array(
'status' => true,
'data' => $data,
'filename' => $filename
);
echo json_encode($result);
wp_die();
}
It lacks a capability check too.
Any logged-in users can export the JSON-encoded data, which includes: WordPress settings, theme and plugins (active/inactive) with their version, Welcart general settings and payment method etc, as well as the server and PHP settings.
Recommendations
Update immediately if you have version 2.2.7 or below installed. If you are using our web application firewall for WordPress, NinjaFirewall WP Edition (free) and NinjaFirewall WP+ Edition (premium), you are protected against this vulnerability.
Timeline
The vulnerability was reported to the developers on July 29, 2021, and a new version 2.2.8 was released on July 31, 2021.
Stay informed about the latest vulnerabilities
- Running WordPress? You can get email notifications about vulnerabilities in the plugins or themes installed on your blog.
- On Twitter: @nintechnet
